Single Sign-On
Users can connect to DefectDojo with a Username and Password, but you can also allow users to authenticate via Single Sign-On (SSO). DefectDojo supports SAML and a range of OAuth providers:
SSO configuration can only be performed by a Superuser.
DefectDojo Pro users: Add the IP addresses of your SAML or SSO services to the Firewall whitelist before setting up SSO. See Firewall Rules for more information.
Disabling Username / Password Login
Once SSO is configured, you may want to disable traditional username/password login.
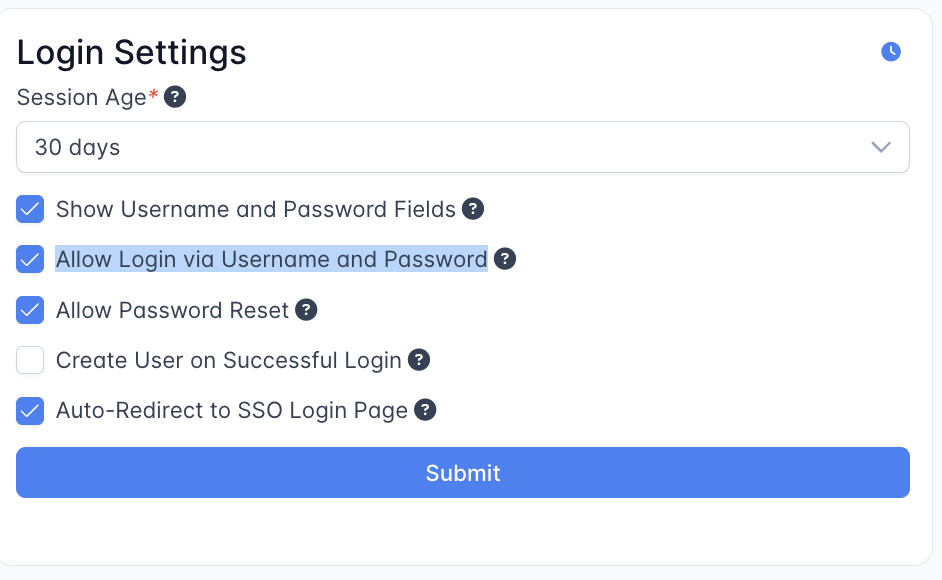
DefectDojo Pro users can uncheck Allow Login via Username and Password under Enterprise Settings > Login Settings.
Open-Source users can set the following environment variables in Docker:
DD_SOCIAL_LOGIN_AUTO_REDIRECT: "true"
DD_SOCIAL_AUTH_SHOW_LOGIN_FORM: "false"Login Fallback
If your SSO integration stops working, you can always return to the standard login form by appending the following to your DefectDojo URL:
/login?force_login_form
We recommend keeping at least one admin account with a username and password configured as a fallback.
Configure Auth0 SSO in DefectDojo Pro
Configure Auth0 SSO in Open-Source DefectDojo
Configure Azure AD SSO and group mapping in DefectDojo Pro
Configure Azure AD SSO and group mapping in Open-Source DefectDojo
Configure GitHub Enterprise SSO in DefectDojo Pro
Configure GitHub Enterprise SSO in Open-Source DefectDojo
Configure GitLab SSO in DefectDojo Pro
Configure GitLab SSO in Open-Source DefectDojo
Configure Google OAuth in DefectDojo Pro
Configure Google OAuth in Open-Source DefectDojo
Configure KeyCloak SSO in DefectDojo Pro
Configure KeyCloak SSO in Open-Source DefectDojo
Configure OpenID Connect (OIDC) SSO in DefectDojo Pro
Configure OpenID Connect (OIDC) SSO in Open-Source DefectDojo
Configure Okta SSO in DefectDojo Pro
Configure Okta SSO in Open-Source DefectDojo
Configure RemoteUser authentication in Open-Source DefectDojo
Configure SAML in DefectDojo Pro
Configure SAML in Open-Source DefectDojo